Agent Governance Runtime
Full power inside.
Full control outside.
Your AI agents get a real computer — full OS, real shell, real tools. The boundary around them controls what they can reach, hides credentials they shouldn't see, and records every move.
Agents are neither software nor users
Software follows orders. People exercise judgment and own the consequences. An AI agent does both — it runs on a computer like software, but reasons, writes its own code, and decides what to execute like a person.
When you hire a new employee, you don't disable their internet. You give them a real workstation and govern through scoped permissions, activity logs, and approval workflows. Unix processes work the same way: full capability, governed by the kernel. So do containers, cloud IAM, and your VPN. The pattern is universal — full capability inside, governed boundary outside.
For agents, the industry hasn't caught up. It's split into two camps — and both fail.
Approach A — Restrict the agent
- Force agents to use predefined tool APIs
- Only allow structured function calls
- Limit what libraries and SDKs they can use
- Hope prompt discipline is enough
Security achieved by crippling the agent.
Approach B — Give broad access
- Run agents in containers with wide permissions
- Pass API keys directly into the environment
- Log informally or not at all
- Rely on humans to catch problems
Capability preserved, ungovernable at scale.
Agents need their own kind of boundary: full capability inside the sandbox, full control on the way out.
Today, you can't answer:
Once agents start touching real systems, the basic operational questions get hard.
What did every agent do last week?
Which agent has access to customer data?
How do we contain the damage when something goes wrong?
How do we prove to auditors what agents did?
How do we stop a misbehaving agent — right now?
How do we cap what each agent can spend?
Ad-hoc IAM, scattered logs, and human supervision work for one agent. They break at ten. They become a liability at a hundred.
The Control Boundary
Every agent runs in its own isolated sandbox with a full operating system. From inside, it looks like a normal computer. From outside, every connection it makes flows through a transparent governance boundary.
The agent doesn't know the boundary is there. It makes normal HTTP calls to normal APIs. The boundary decides whether the call is allowed, attaches the right credentials, records what happened, and either lets it through or stops it cold.
Enforced by infrastructure — not by application code
Transparent gateway
Every outbound call passes through a gateway you control. No bypass, no escape, no DNS trick. The agent never knows it's there.
Hidden credentials
Agents never hold API keys. The gateway attaches them only at the moment of the call. If the agent is compromised, your credentials aren't.
Complete audit
Every action recorded: who, where, with what credentials, with what result. Queryable, exportable, complete.
Spending caps
Set request and cost limits per agent and per capability. The gateway enforces them so a runaway agent can't run away.
Per-task identity
Every task gets its own short-lived cryptographic identity. Every action is attributable to a specific agent, role, and run.
Domain control
Each agent's world is shaped by an allowlist. Anything outside doesn't resolve. Locked down by default.
The four moments of governance
Configure, watch, analyze, audit — one console for the full lifecycle.
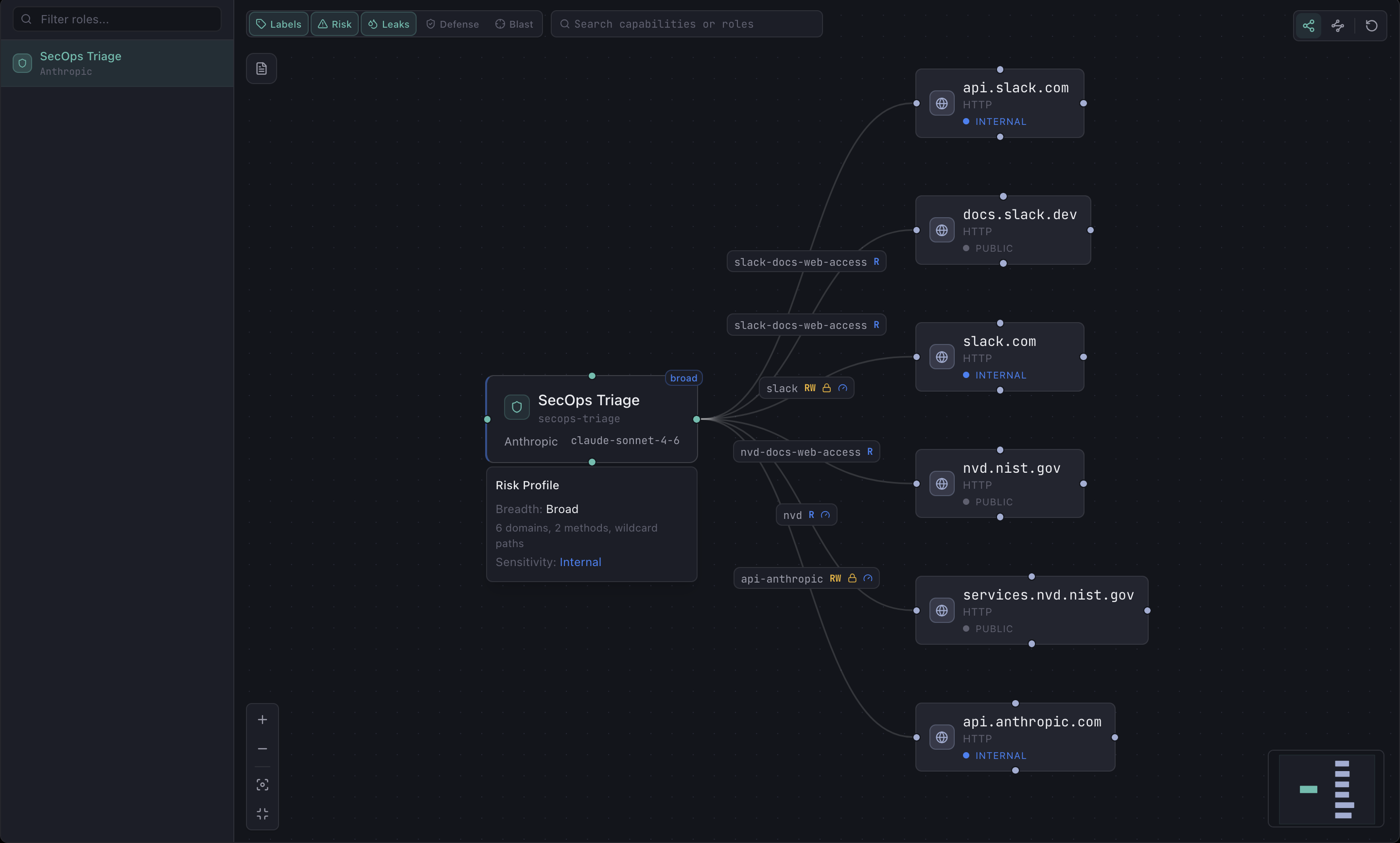
Design the boundary — before the agent runs.
Define each role's reach: what domains, what methods, what budgets. See the full topology and risk profile in one view.
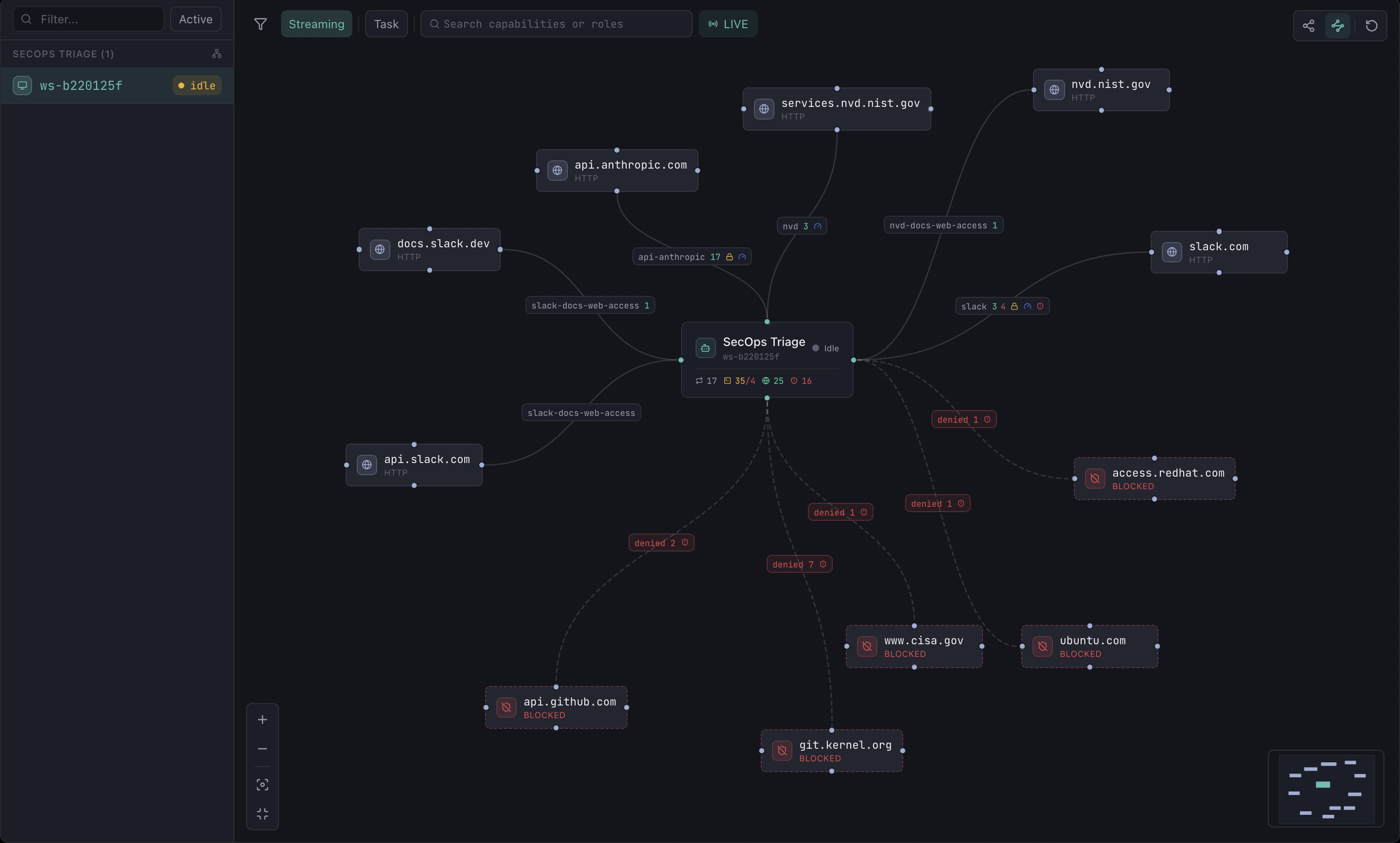
Watch the boundary work — while agents run.
A live view of every running agent, every connection they're making, and every policy decision — as it happens.
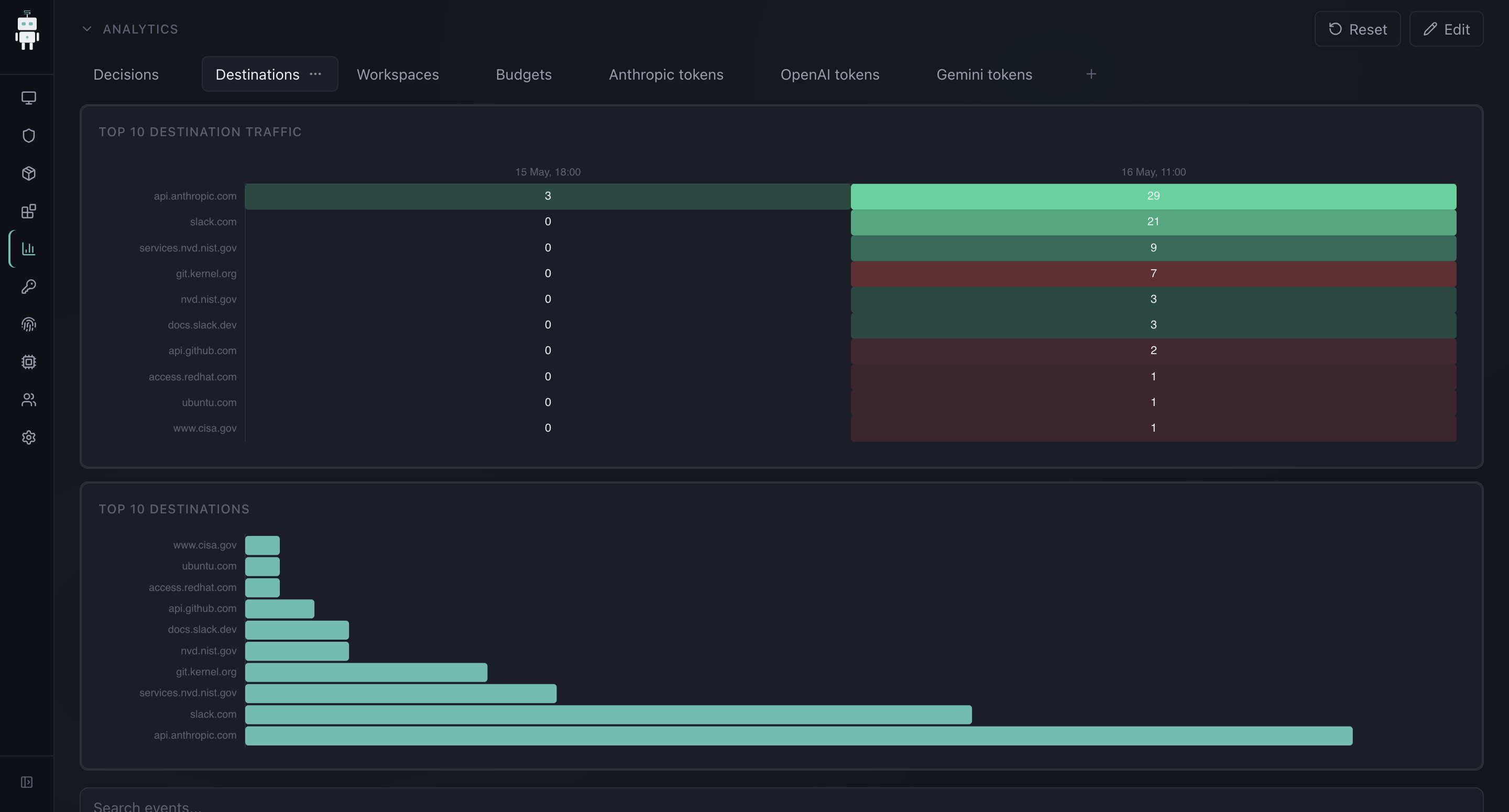
Understand the whole fleet
Traffic, denials, token usage, costs — broken down by destination, agent, and workspace. Filter, slice, and export.
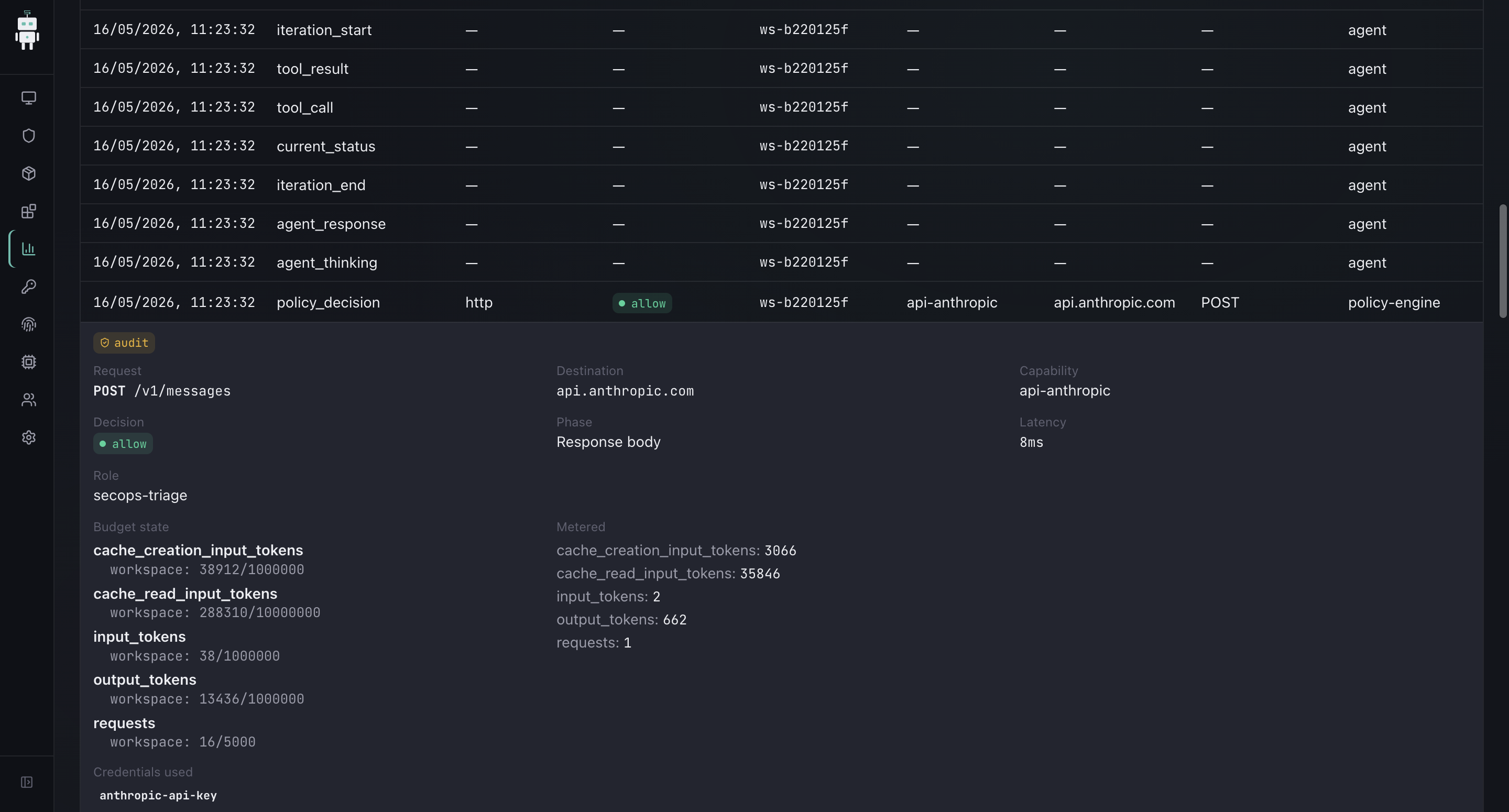
Drill into any action — ever.
Every request is kept with full context: identity, destination, response, latency, cost. The answer to "what did the agent do?" is one query away.
Governance doesn't restrict.
It unlocks.
When the boundary is real — when it's the network, not the prompt — your agents can hold real capabilities without holding real risk.
Start where it's painful. When a new CVE lands that touches your stack, the agent reads it, queries your asset inventory, and reports back: does this affect us, where, and how badly. That hour-long manual check — done in seconds, with a full audit trail.
Then give it a playbook. If the CVE is real, the agent drafts patch tickets, pings on-call, and — for critical issues with a known mitigation — applies the workaround and writes up what it did and why.
The triage agent itself has no permission to reach Slack. It delegates to a second agent whose entire allowed surface is one channel — and nothing else. Each agent's reach is exactly what its job needs, and no more.
Same governance the whole way. From answering one question to driving an autonomous triage loop, every action is recorded and every boundary enforced.
Built on infrastructure your team already trusts
Ready to govern your agents?
Tell us about your stack — we'll find a time to walk through how SAWP fits.
Not ready for a call?Get product updates instead →